Get the latest news delivered right to your email.
2024 Election
Top Stories
Advertisement
Biden Gets Even More Delusional, Says He Can Win Red State That He Lost
It was a strange assertion from the president in light of both history and available data, but we should not have expected otherwise.
By Michael Schwarz
April 25, 2024
Comment
MoreShare
Secret Document: Plans Being Made to Pave the Way for US Troops to Fight in Eastern Europe
"NATO officials are increasingly concerned about Vladimir Putin launching an incursion on NATO’s eastern flank."
By George C. Upper III
April 25, 2024
Comment
MoreShare
The 'Chilling' Final Monologue Tucker Carlson Prepared for Fox News Has Been Released for the First Time
"Carlson planned to discuss members of the government lobbying to have his show taken off the air,” his biographer said.
By Jack Davis
April 25, 2024
Comment
MoreShare
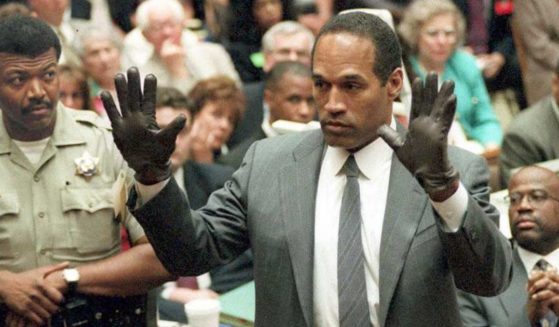
'You've Got to Be Kidding': Upcoming O.J. Simpson Biopic Reaches New Low for Hollywood, Depicts Him as Innocent
Only in Hollywood would a project claiming O.J. Simpson was an innocent man ever come close to taking shape.
By Jack Davis
April 25, 2024
Comment
MoreShare
Foreign Students Who Get Suspended for Anti-Israel Activities Could Face Even Tougher Punishment, DHS Confirms
Foreign students who join in anti-Israel protests at colleges and are suspended could face some major consequences.
By Jack Davis
April 25, 2024
Comment
MoreShare
Report: Family Outraged at Disney World - Realized the Evil Queen 'Actress' They Took Pics with Was a Man
A father was outraged when it appeared that Walt Disney World reportedly hired a man to interact with children as the Evil Queen.
By Allison Anton
April 24, 2024
Comment
MoreShare
Interviewer's Simple Question Gets NYU Protester to Admit She Has No Idea What's Going On: 'I Wish I Was More Educated'
These protesters didn't even try to act as if they knew the reasons they were protesting NYU at all, admitting ignorance almost immediately.
By Allison Anton
April 24, 2024
Comment
MoreShare
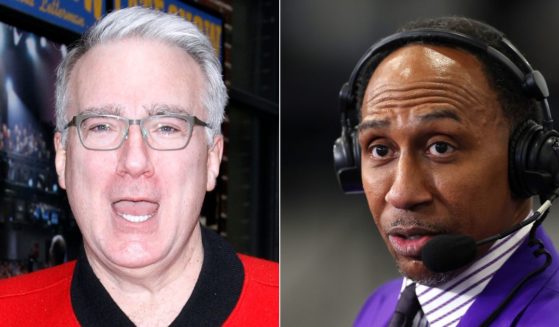
Keith Olbermann Issues Ultimatum to ESPN: Silence or Fire Stephen A. Smith After Trump Comments
Smith has faced considerable backlash for saying that Donald Trump "wasn't lying" when he said black Americans find him relatable.
By Anthony Altomari
April 24, 2024
Comment
MoreShare
Advertisement
'Woman': The Left's Absurd Quest to Redefine the Term
The question “What is a woman?” is perfectly leveraged to produce absurdity because to pose this question is absurd.
Comment
MoreShare
Biden Breaking the Ten Commandments: Part Four - Bidenomics Subverts the Sabbath
Biden is upsetting the balance of rest and work ordered by God — and Americans are paying the price economically and spiritually.
Comment
MoreShare
Former Military Chaplain Talks Becoming Battle-Ready to Serve in God's End-Times Army
U.S. Army Col. (Ret.) David Giammona believes the world is entering the end times, and "the Lord wants us to work even harder."
Comment
MoreShare
Advertisement